Your visitors land on your website and see a bold red screen instead of your homepage. The Deceptive Site Ahead warning instantly destroys trust and drives traffic away. In seconds, you can lose leads, sales, and credibility.
This alert usually appears when Google detects malware, phishing content, or suspicious code on your site. The good news is that you can fix it.
With the right steps, you can remove the warning, secure your website, and quickly restore your online reputation.
TL;DR: Resolving Deceptive Site Ahead Warning Fast
- The warning appears when Google detects phishing, malware, SSL issues, or deceptive content on your site.
- Scan your website, remove malware, fix vulnerabilities, and eliminate fake plugins or backdoors immediately.
- Use trusted security plugins or hire professionals to ensure complete cleanup and prevent reinfection.
- Submit a review request in Google Search Console after fixing issues and strengthening security to avoid future warnings.
What is the Deceptive Site Ahead Warning?
The ‘Deceptive Site Ahead’ warning, or deceptive website warning sign, is a security feature implemented by browsers like Google Chrome.
It protects users from accessing potentially harmful websites. When this warning appears, it means the website you’re trying to access may be compromised or contain malicious content, such as phishing or malware.
The dangerous site warning alerts users before they enter a website that could potentially harm their device or steal sensitive information.
This is particularly important in today’s digital age, where online threats are becoming increasingly sophisticated. The warning can appear in different forms, depending on the browser.
For instance, in Google Chrome, the warning will appear as a red screen with a warning message. Whereas, in Mozilla Firefox, it will appear as a yellow warning bar.
Receiving a ‘Deceptive Site Ahead’ warning can be a serious issue for website owners, as it can lead to a loss of trust and credibility with their visitors.
It’s important to address the issue promptly to prevent further damage to the website’s online reputation.
Get Your Website Rid of All Malware in No Time!
We are experts in repairing hacked WordPress websites and can help you get rid of all online threats, including malware, at speed.
Understanding Website Warning Messages
Encountering a warning message while browsing can be alarming, but each message carries specific implications that can help you address underlying issues effectively.

Here’s a closer look at common warnings and their meanings:
Deceptive Site Ahead
This warning indicates potential phishing activity. It suggests that a website may impersonate a legitimate site to trick users into disclosing personal information. It leads to a digital trap set to capture unsuspecting visitors.
Site Contains Malware
When confronted with this alert, it signals the presence of malicious software on the website. Malware can impact various site elements, including images, ads, or third-party segments, posing a risk to visitors’ devices and data security.
Learn More: Malware Removal Services vs Website Security Services
Suspicious Site
A more general cautionary message, signaling Google’s detection of suspicious or potentially unsafe activity on the website. It suggests taking caution before proceeding further on the site.
Site Ahead Contains Harmful Programs
This warning advises users about the possibility of encountering harmful programs that could disrupt their browsing experience or compromise their device’s security. It serves as a potential measure to prevent possible harm.
This Page is Trying to Load Scripts from Unauthenticated Sources
While not as severe as other warnings, this message highlights a security oversight. It indicates a secure (HTTPS) website attempts to load content from unsecured (HTTP) sources. It doesn’t necessarily mean a breach but highlights the importance of securely hosting all website resources.
Did You Mean [Site Name]?
Google displays this message if it suspects a user may have mistyped a website address, potentially leading them to a fraudulent or misleading site. It’s a cautionary prompt to verify the intended destination before proceeding.
For website owners encountering this warning, Google provides a specific form to address misunderstandings or misidentifications.
Browser-Specific Messages
Safari’s “Fraudulent Website Warning” and Firefox’s “Potential Security Risk Ahead” function similarly to Google’s warnings, even though they have slightly different wording. Despite variations in presentation, the underlying causes and resolution methods remain consistent across browsers.
In all cases, the recommended course of action involves addressing any security vulnerabilities or deceptive practices on the website. It is about requesting a review from Google or the respective browser’s support team.
Learn: How to Protect Your WordPress Site from Malware
How to Clear Your Website of Malware and Get Rid of the Common Malware Warnings
Clearing your website of malware is crucial not just for removing Google’s “Deceptive Site Ahead” warning but also for ensuring safety from other potential hazards.
Here’s how you can tackle this issue in three straightforward steps:
- Start by thoroughly checking your website for any malicious software. This step is about identifying all the unwanted guests lurking in the corners of your site.
- Once you’ve identified the malware, the next step is to carefully remove it from your site. This process needs to be handled with care to avoid any additional damage to your website.
- After cleaning your site, the final step is to ask Google to review your site. This is how you get the malware warning message removed by proving that your site is clean and safe again.
Key Considerations:
Before diving into this process, there are some critical points you should keep in mind:
- Speed is Key: Delaying the removal of malware can have severe consequences. This allows the malware to cause more damage but also negatively impacts Google’s perception of your site. Act quickly to resolve these issues.
- Malware Removal Can Be Tricky: If you’re not confident in your technical skills, especially with platforms like WordPress, think twice before attempting a DIY malware removal. A misstep here can lead to further issues, potentially breaking your site.
- Address the Root Cause: It’s essential to understand why your website was compromised in the first place. In most cases, vulnerabilities or backdoors allow hackers in. Simply cleaning the malware without fixing these issues means you could get reinfected.
Lastly, the internet is full of tips and tricks, but not all of them are good or applicable to your situation. Following incorrect guidance can sometimes do more harm than good, leading to even bigger problems for your website.
Why Does Google Flag Dangerous Websites?
Google flags dangerous sites to protect users from harm. The search giant’s priority is to ensure that users have a safe and secure browsing experience.
Google employs sophisticated algorithms to detect websites that are involved in phishing, malware distribution, and other malicious activities.
These algorithms work in real-time and are constantly updated to catch new threats as they emerge.
Google’s flagging system also helps to hold website owners accountable for their content. If a website is found to be hosting malicious content or engaging in other harmful activities, Google will take steps to penalize the site. This can include removing the site from search results or even de-indexing the site entirely.
Google’s flagging of dangerous sites is a crucial part of its efforts to provide a safe and secure browsing experience for users.
By being vigilant and staying up-to-date with the latest threats, Google is able to keep users safe and maintain the integrity of the web.
Do not miss: Learn How to Remove Malware from WordPress Site
What Causes the Deceptive Site Warning to Appear?
The “Deceptive Site Ahead” warning is a browser-generated alert that signals a potential threat to users attempting to access a particular website.
This warning is a protective measure, designed to safeguard users from various forms of online dangers such as phishing, malware, and social engineering attacks.
But what exactly causes this warning to appear, and how can website owners prevent it?
Expired or Misconfigured SSL/TLS Certificates
SSL/TLS certificates are crucial for establishing a secure connection between a website and its visitors.
They encrypt the data transmitted between the browser and the server, protecting sensitive information like passwords, credit card numbers, and personal details.
However, when an installed SSL/TLS certificate expires or is not properly configured, it can lead to security vulnerabilities.
Browsers may interpret this as a sign of potential danger and trigger a “Deceptive Site Ahead” warning to prevent users from accessing a site that may not be secure.
Phishing Attacks
Phishing is one of the most common types of social engineering attacks, where malicious entities create websites that appear legitimate but are designed to steal sensitive information.
For instance, a user might land on a website that looks exactly like their bank’s login page but is actually a cleverly disguised trap set to harvest their credentials.
These fake sites often use deceptive URLs that closely resemble those of trusted entities. When browsers detect such suspicious activities, they issue a warning to protect users from falling victim to these scams.
Malware Infections
Malware refers to any software intentionally designed to cause damage to a computer, server, or network. Websites infected with malware can pose significant risks to visitors, from spreading viruses to stealing personal data.
Often, hackers inject malicious code into legitimate websites without the owner’s knowledge. This code can then execute harmful actions when a visitor accesses the site, prompting the browser to issue a warning.
Removing malware promptly and securing your site against future attacks is crucial to maintaining its integrity.
Deceptive Content
Deceptive content refers to any material on a website that misleads users into performing actions they wouldn’t normally take, such as downloading software, sharing personal information, or making payments.
This content often masquerades as legitimate pop-ups or ads, falsely claiming that a user’s software is outdated or that their device is at risk.
Deceptive content is particularly insidious because it exploits the trust users place in what appears to be a credible source, leading to unintended and often harmful consequences.
Examples of Social Engineering Violations:
To better understand what might cause your site to be flagged, consider these examples:
Deceptive Content:
- Pop-ups intended to trick users into installing malware.
- Fake browser update notifications.
- Fake login pages that mimic trusted entities to steal credentials.
Deceptive Ads:
- Ads that masquerade as legitimate page interface elements, like action buttons.
- Pop-ups claiming software is out of date, prompting downloads of unwanted software.
Insufficiently Labeled Third-Party Services
In some cases, websites utilize third-party services for various functions, such as payment processing or customer support.
If the relationship between the primary website and the third-party service isn’t clearly communicated to users, it can create confusion and potentially lead to social engineering attacks.
For example, if a non profit organization website uses a third-party platform for donations but fails to make this relationship clear, users might be unsure about who they are sharing their payment information with, leading to distrust or even a security flag from the browser.
Impact of the Deceptive Site Ahead Warning on Your Website
The dangerous website or ‘Deceptive Site Ahead’ warning sign can have a significant impact on your website.
- First and foremost, the warning can scare off potential visitors to your website. If users see the warning, they may think your website is not trustworthy or safe and choose to navigate away.
- Additionally, the warning can harm your website’s reputation and credibility. If users see the warning, they may assume that your website has been compromised or hacked, which can damage your brand image.
- The warning can also negatively impact your website’s SEO. Search engines such as Google prioritize secure websites, and the ‘Deceptive Site Ahead’ warning can signal to search engines that your website is not secure, which can result in a lower search engine ranking.
- Furthermore, if the warning is due to a malware infection or phishing attack, your website’s visitors may become victims of identity theft or financial fraud. This can result in legal action and damage to your business’s reputation.
It’s crucial to take the ‘Deceptive Site Ahead’ warning seriously and take steps to fix the issue as soon as possible. By doing so, you can protect your website’s reputation, credibility, and the safety of your visitors.
How to Identify the Source of ‘Deceptive Site Ahead’ Warning?
Identifying the source of the ‘Deceptive Site Ahead’ warning is the first step in fixing the issue. There are several ways to identify the problem, depending on the cause of the warning.
- If the warning is due to an expired or incorrectly installed SSL/TLS certificate, you can check the certificate’s status by clicking on the padlock icon in the browser’s address bar. This will display information about the certificate’s validity and issuer.
- If the certificate has expired or is not issued by a trusted authority, it will trigger a warning.
- If the warning is due to a phishing attack, you can use Google’s Safe Browsing tool to check if your website has been flagged as a phishing site. Safe Browsing is a free tool that helps website owners identify security issues on their websites.
- If your website has been flagged, Safe Browsing will provide information on the specific issues that triggered the warning.
- If the warning is due to a malware infection, you can use a malware scanner to scan your website for malicious code. There are several free and paid malware scanners available. These scanners will scan your website for malware and provide you with a report of any issues found.
- Lastly, if the warning is due to third-party plugins or widgets, you can try disabling them one by one to identify the specific plugin or widget causing the issue.
Once you’ve identified the source of the problem, you can take the necessary steps to fix it.
Fixing the ‘Deceptive Site Ahead’ Warning
Once you’ve identified the source of the ‘Deceptive Site Ahead’ warning, it’s time to take steps to fix the issue.
The first step in fixing the dangerous site or ‘Deceptive Site Ahead’ warning sign is to scan your website for malware.
Malware is malicious software that can infect your website and cause security issues, including triggering the ‘Deceptive Site Ahead’ warnings.
There are several ways to scan your website for malware, including:
- Deep scan your website: A deep scan is a comprehensive scan that checks all files and folders on your website. This can help identify any hidden malware by a surface-level scan.
- Use an online scanner: Several are available. These scanners will scan your website for malware and provide you with a report of any issues found.
- Scanning manually: You can also manually scan your website by following these steps:
- Visit your website from an incognito browser: This will prevent any cached files from affecting the scan results.
- Check the number of pages indexed on Google: If the number is higher than expected, it may indicate that your website has been hacked and additional pages have been added without your knowledge.
- Look for unusual user activity logs: Check your website’s user activity logs for any unusual activity, such as logins from unfamiliar IP addresses or suspicious user behavior.
- Check for strange trends in analytics data: Look for unusual spikes or dips in website traffic or engagement, which may indicate a security issue.
- Look for Google Search Console warnings: Google Search Console will notify you of any security issues detected on your website.
- Remove nulled plugins: Nulled plugins might sound cool in the beginning but you never know at what point they will harm your website to the level that you may lose your entire business.
Effective Methods to Remove the Deceptive Site Ahead Warning
If your website is flagged, you need a clear action plan to restore security and trust. Below are three proven methods to eliminate malware and fix the warning efficiently.
Method 1: Use a Security Service to Remove Malware
Take the hassle out of removing malware with these user-friendly security plugins.
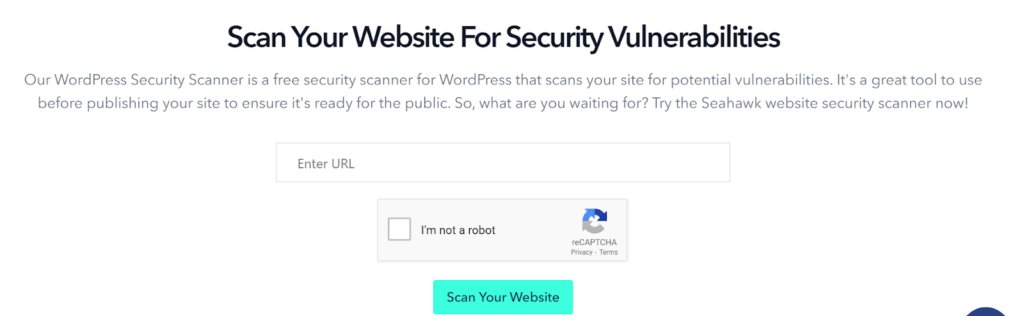
Seahawk’s WordPress Security Scanner
Use our own WordPress Security Scan tool to identify problems with your website. Whether your site has malware issues, Search console issues, or Google deceptive site ahead notifications; identify all of them with our scanner and have them resolved with our dedicated service in record time.
WordFence Security Plugin
WordFence Security is a popular WordPress plugin designed to enhance the security of WordPress websites. It provides a wide range of security features such as malware scanning, firewall protection, login security, and more.
One of the main features of WordFence is its malware scanner, which is designed to detect and remove malware from WordPress sites. The plugin scans the website files and databases for any signs of malicious code or activity.

It also checks the website against known vulnerabilities and compares the files to the original WordPress files to check for any changes.
If the scanner detects any malware, WordFence will alert the site administrator and provide instructions on how to remove the malware. The plugin also offers an option to automatically remove the malware if the site administrator chooses to do so.
In addition to the malware scanner, WordFence also offers other features such as a firewall that can block malicious traffic and protect against brute-force attacks. It also has a login security feature that allows site administrators to set rules for strong passwords and limit the number of login attempts.
If you opt to upgrade to WordFence premium, it will cost you $99-$950 per year which will give you access to real-time IP and country blocking features, stopping all requests from malicious IP addresses or countries of your choice.
Method 2: Clean Your Website Manually
If you’re looking to clean your website manually, here is the guide.
Take a Backup of Your Website
The first step in cleaning your website manually is to take a backup of your website. This is a crucial step that ensures you have a restore point if something goes wrong during the cleaning process.
To back up your website, you can use a plugin such as BlogVault, which lets you back up and restore your site with ease.
Alternatively, you can use your web hosting provider’s backup service or manually back up your website by downloading all the files via FTP and exporting the database using phpMyAdmin.
It’s important to store your backup files in a secure location, such as an external hard drive or cloud storage service.
Check for Fake Plugins
The second step in cleaning your website manually is to check for fake and nulled plugins. These are plugins that are either pirated or modified versions of legitimate plugins and can contain malicious code that can compromise the security of your website.
To check for fake and nulled plugins, you should start by reviewing the list of plugins installed on your website.
You can do this by navigating to the “Plugins” section in your WordPress dashboard. Look for any plugins that you don’t recognize or that have suspicious names or descriptions.
Next, you should check the source of the plugins. Only download plugins from reputable sources such as the official WordPress repository or the plugin author’s website.
Avoid downloading plugins from third-party websites, as these may be fake or nulled versions.
If you find any fake or nulled plugins, you should remove them immediately.
Reinstall WordPress
The third step in cleaning your website manually is to reinstall WordPress. Reinstalling WordPress is a drastic step, here’s how you do it through cPanel
- Log in to your cPanel account.
- Navigate to the “Softaculous Apps Installer” section and click on the WordPress icon.
- Click on the “Remove Installation” button to completely remove your current WordPress installation.
- Once the removal process is complete, click on the “Install” button to start the WordPress installation process.
- Fill in the required information, such as your website name, description, and administrator username and password.
- Select your preferred WordPress version and language.
- Click on the “Install” button to begin the installation process.
Once the installation process is complete, you will be able to log in to your WordPress dashboard with the administrator username and password you set during the installation process.
Don’t forget to update all your plugins and themes to their latest versions and change all your passwords, as described in step 3 above.
Reinstalling WordPress through cPanel is a quick and easy way to completely clean your website of any malware or other security threats that may be causing the ‘Deceptive Site Ahead’ warning to appear.
Clean Plugin and Theme Folders
The fourth step in cleaning your website manually is to clean the plugin and theme folders. Malicious code can often be hidden in the files of your website’s plugins and themes, so it’s important to thoroughly clean these folders.
To clean your plugin and theme folders, follow these steps:
- Log in to your website’s FTP account or use cPanel’s file manager to access your website’s files.
- Navigate to the “wp-content” folder.
- Within the “wp-content” folder, you will see two folders named “plugins” and “themes”. Open each of these folders and examine the contents.
- Delete any plugins or themes that you don’t recognize or that you suspect may be causing the Deceptive Site Ahead warning to appear. Be careful not to delete any plugins or themes that are essential to your website’s functionality.
- For the remaining plugins and themes, open each file individually and examine the code.
- Look for any suspicious code that may be causing the issue. If you are not sure what to look for, consider seeking the help of a security expert.
Once you have deleted any suspicious plugins and themes and cleaned the code of the remaining files, your website should be free of any malicious code that may be causing the Deceptive Site Ahead warning to appear.
Remember to keep all your plugins and themes updated to their latest versions to prevent future security threats.
Clean Malware from the Database
The fifth step in cleaning your website manually is to clean malware from the database. Malicious code can also be hidden in your website’s database, so it’s important to clean it thoroughly.
To clean malware from the database, follow these steps:
- Log in to your website’s cPanel.
- Navigate to the “phpMyAdmin” section.
- Select your website’s database from the list of databases.
- Click on the “Check All” checkbox to select all the tables in your database.
- Click on the “Repair Table” button to repair any corrupted tables in the database.
- Next, click on the “SQL” tab at the top of the page.
- In the SQL query box, enter the following command:
SELECT * FROM wp_options WHERE option_name = ‘active_plugins’;
This command will display a list of all the active plugins on your website.
- Look for any suspicious plugins that you don’t recognize or that you suspect may be causing the Deceptive Site Ahead warning to appear.
- Replace “suspicious-plugin-folder-name” with the name of the suspicious plugin’s folder.
- Repeat the above-mentioned 8th and 9th points for all the suspicious plugins.
- Finally, run a malware scan on your website to ensure that all the malicious code has been removed.
Cleaning the database manually can be a complex and time-consuming process, so it’s recommended that you seek the help of a security expert if you’re not familiar with this process.
Know More: Best WordPress Security Service Providers
Remove All Backdoors
Backdoors are hidden entrances to your website that hackers can use to gain access to your site even after you’ve cleaned it.
To remove all backdoors from your website, follow these steps:
- Log in to your website’s cPanel.
- Navigate to the “File Manager” section.
- Locate the root directory of your website.
- Look for any suspicious files or folders that you don’t recognize or that have strange names.
- Delete any suspicious files or folders.
- Look for any new files or folders that were not present before you started cleaning your website. These could be backdoors that were created by the hacker.
- Delete any new files or folders.
- Change all your website passwords, including your WordPress admin password, FTP password, cPanel password, and any other passwords associated with your website.
Reupload Your Cleaned Files
After you’ve completed all the steps to clean your website manually, the next step is to re-upload your cleaned files to your website’s server.
To re-upload your cleaned files, follow these steps:
- Log in to your website’s cPanel.
- Navigate to the “File Manager” section.
- Locate the root directory of your website.
- Upload the cleaned WordPress files to your website’s root directory using an FTP client like FileZilla or through the “File Manager” in cPanel.
- Once the upload is complete, make sure that all the files have been uploaded successfully and that there are no errors or missing files.
Clear the Cache
Once you’ve reuploaded your cleaned files, the next step is to clear the cache of your website to ensure that all the changes take effect.
Here’s how to clear the cache of your website:
- Log in to your WordPress dashboard.
- Navigate to the “Plugins” section.
- Find and activate a cache plugin, such as W3 Total Cache or WP Super Cache.
- Navigate to the cache settings and clear the cache.
- If you don’t have a cache plugin installed, you can clear the cache by navigating to the “Settings” section of your WordPress dashboard, then selecting “Permalinks” and clicking “Save Changes.” This will clear the cache and rebuild your website’s permalinks.
Clearing the cache will ensure that your website’s visitors see the updated, cleaned version of your website without any lingering malware or infected files.
Use a Security Scanner to Confirm That the Malware is Completely Gone
Using a security scanner is the final step to confirm that the malware is completely removed from your website.
It’s important to be certain that your website is clean before you remove the “Deceptive Site Ahead” warning, as failing to do so could lead to the warning reappearing.
Here’s how to use a security scanner to confirm that your website is free of malware:
- Choose a reputable security scanner, such as Seahawk’s Security Scanner
- Run a deep scan of your website to detect any remaining malware or infected files.
- Review the scanner’s report to identify any remaining issues.
- If the scanner detects any malware or infected files, repeat the previous steps to clean your website.
- Once the security scanner confirms that your website is clean, you can proceed to remove the “Deceptive Site Ahead” warning.
Using a security scanner ensures that your website is free of malware, providing peace of mind for you and your website’s visitors.
Why You Should Avoid Manually Cleaning a Hacked WordPress Site?
While cleaning a hacked WordPress site manually may seem like a good idea, it’s important to be aware of the potential risks involved.
There are several reasons why you should avoid manually cleaning a hacked WordPress site, including:
- Lack of expertise: If you’re not familiar with the inner workings of WordPress, you may not know where to look for malware or how to identify malicious code. This can lead to missed infections or incomplete cleanups, leaving your website vulnerable to further attacks.
- Increased risk of error: Even if you do know your way around WordPress, manual cleaning is a time-consuming and error-prone process. One misplaced character or overlooked file could cause your website to break or even crash, leading to costly downtime and lost revenue.
- Malware reinfection: Even if you think you’ve cleaned your website thoroughly, it’s possible that malware could still be hiding in obscure corners of your website. Without the proper tools and expertise, you may not be able to detect or remove all instances of malware, leaving your website vulnerable to reinfection.
Basically, manually cleaning a hacked WordPress site can be a risky and time-consuming process.
To ensure the best possible outcome, it’s often recommended to seek the help of a professional security service that specializes in WordPress security.
They have the expertise and tools necessary to clean your website thoroughly. They can also help ensure that your website stays protected against future attacks.
Method 3: Hire a Professional WordPress Security Service
While there are many WordPress security plugins available that can help detect and remove malware from your website, sometimes the issue can be more complex and require a deeper level of expertise.

Hiring a WordPress security expert is often the best way to solve the “deceptive site ahead” issue because they have the knowledge and experience to thoroughly investigate and diagnose the problem.
Seahawk performs a detailed analysis of your website and identifies any vulnerabilities that may be causing the issue. We also conduct a thorough malware scan and remove any malicious code that may be present.
Additionally, we take steps to tighten your website’s security, such as updating software, implementing stronger access controls, and many more.
Method 4: Remove ‘Deceptive Site Ahead’ Warning via Google Search Console
Here are the steps to remove the ‘Deceptive Site Ahead’ warning by submitting a review request to Google:
- Sign in to Google Search Console: Visit the Google Search Console website and log in with your Google account. If your website is not already added, you will need to verify ownership and add it to the Search Console.
- Navigate to Security Issues: Once you’re logged in, navigate to the ‘Security Issues’ section under the ‘Security & Manual Actions’ tab. This is where Google will provide details on any security issues found on your website, including the ‘Deceptive Site Ahead’ warning.
- Review the Security Issue: Click on the issue to view more details about the warning. Google will provide information about the type of issue found and the URLs that were affected.
- Fix the Security Issue: Follow the steps provided by Google to fix the security issue on your website. Once you’ve made the necessary changes, Google will automatically start the review process.
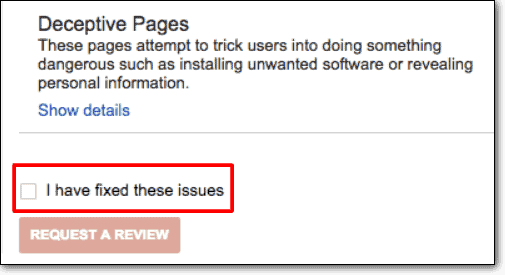
- Request a Review: After you’ve fixed the security issue, click on the ‘Request a Review’ button in the ‘Security Issues’ section. This will submit your website for review by Google.
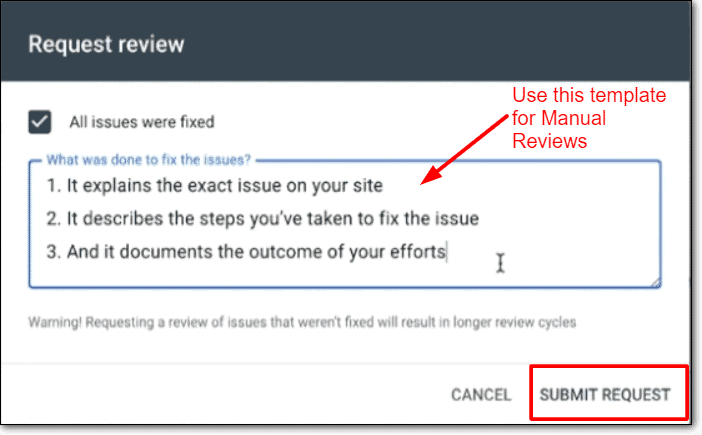
- Wait for Review: Google will review your website to ensure that the security issue has been fixed. This process can take anywhere from a few days to a few weeks.
- Receiving the Verification: If the review is successful, Google will remove the ‘Deceptive Site Ahead’ warning from your website. You’ll receive a notification in the ‘Security Issues’ section of the Search Console.
How to Prevent the Deceptive Site Ahead Error Message from Reappearing in the Future?
To prevent the Deceptive Site Ahead error message from reappearing, you need to take a few security measures. Here are some tips:
- Keep everything up-to-date: Ensure that you keep your website’s themes, plugins, and WordPress versions updated. This helps to patch any security vulnerabilities that may have been discovered.
- Use reputable themes and plugins: Only use themes and plugins from reputable sources. Free themes and plugins can be tempting, but they often come with security risks.
- Use strong passwords: Use strong passwords for all your user accounts, including your WordPress admin account. Weak passwords can be easily hacked.
- Install a security plugin: Use a security plugin to add an extra layer of security to your website. The plugin can scan your website for malware and suspicious activity, block malicious IP addresses, and provide other security features.
- Enable HTTPS: Enable HTTPS on your website to encrypt communication between the website and the user’s browser. This helps to prevent man-in-the-middle attacks and other security vulnerabilities.
- Use a web application firewall (WAF): A WAF can help block attacks before they reach your website. It can also block malicious traffic, such as bots and spam.
By following these steps, you can significantly reduce the risk of website hack and the Deceptive Site Ahead error message from reappearing.
Conclusion
In conclusion, receiving a ‘Deceptive Site Ahead’ warning can be alarming. But, it’s important to take immediate action to fix the issue. By following the steps we have outlined, you can clean your website of any malware. Thereby, preventing the warning from reappearing in the future.
Using a reliable security plugin can also help you with the process. Thus, ensuring your website is safe against potential threats.
However, we do not recommend going for manual cleaning if you’re not a WordPress Pro. But does that mean you can’t get rid of the malware? Definitely not!
If you are struggling with the issue or need professional assistance, consider Seahawk, WordPress experts as your go-to solution for deceptive site-ahead malware removal.
Remember, keeping your website secure is crucial for maintaining the trust of your visitors and protecting your online reputation.
Don’t wait until it’s too late. Take action now to keep your website safe and secure. Connect with us today!
Deceptive Site Ahead FAQs
Why does Google say my site is dangerous?
If Google labels your site as dangerous, it means that their automated systems or user reports have detected potential threats, security vulnerabilities, or malicious activities on your website.
This could include malware distribution, phishing attempts, or other harmful content. Google issues warnings to protect users from potential harm.
It also recommends website owners to address the identified issues to ensure a safe browsing experience for visitors.
Why am I getting warnings about websites?
Web browsers or security software often issue warnings about websites to inform users about potential risks associated with a particular website.
These warnings may be triggered by factors such as malware presence, phishing attempts, suspicious content, or deceptive practices on the site.
Users should exercise caution or avoid interacting with flagged websites to protect their online security.
What does a deceptive warning mean?
A deceptive warning typically refers to a cautionary message or alert indicating that a website or online content may be misleading, fraudulent, or could potentially engage in deceptive practices.
It warns users that the site’s content or activities may not be what they appear to be, potentially posing risks such as scams or malicious behavior.
What is a ‘Deceptive Site Ahead’ warning?
The ‘Deceptive Site Ahead’ warning actively alerts users about flagged websites that contain malware, phishing scams, or other harmful content.
This security feature protects visitors by warning them of potential threats that could damage their computers or compromise their personal information.
How does the warning affect website traffic?
The ‘Deceptive Site Ahead’ warning can severely impact website traffic and user trust. Visitors are likely to leave the site immediately upon seeing the warning, leading to a decline in website traffic, reputation, and revenue.
How can I prevent future warnings from appearing?
You can prevent future warnings by regularly scanning your website for malware, keeping your software and plugins up-to-date, using strong login credentials, and installing a website security plugin.
Will my website be penalized by search engines if I receive a warning?
If your website receives a ‘Deceptive Site Ahead’ warning, it may lead to a drop in search engine rankings and a decrease in website traffic. However, if you fix the issue promptly, your website can recover from the penalty.
Can I remove the warning myself or do I need to seek professional help?
You can remove the warning yourself, but it requires technical expertise and knowledge of website security. Alternatively, you can seek professional help from a website security expert.